Fellow Dockers,
Today we are happy to introduce Docker 0.9. With this release we are continuing our focus on quality over features, shrinking and stabilizing the core, and providing first-class support for all major operating systems.
In addition to dozen of bug fixes, Docker 0.9 includes 2 major improvements: execution drivers and libcontainer.
As usual, for a complete list of improvements, you can check out the Changelog.
Execution drivers
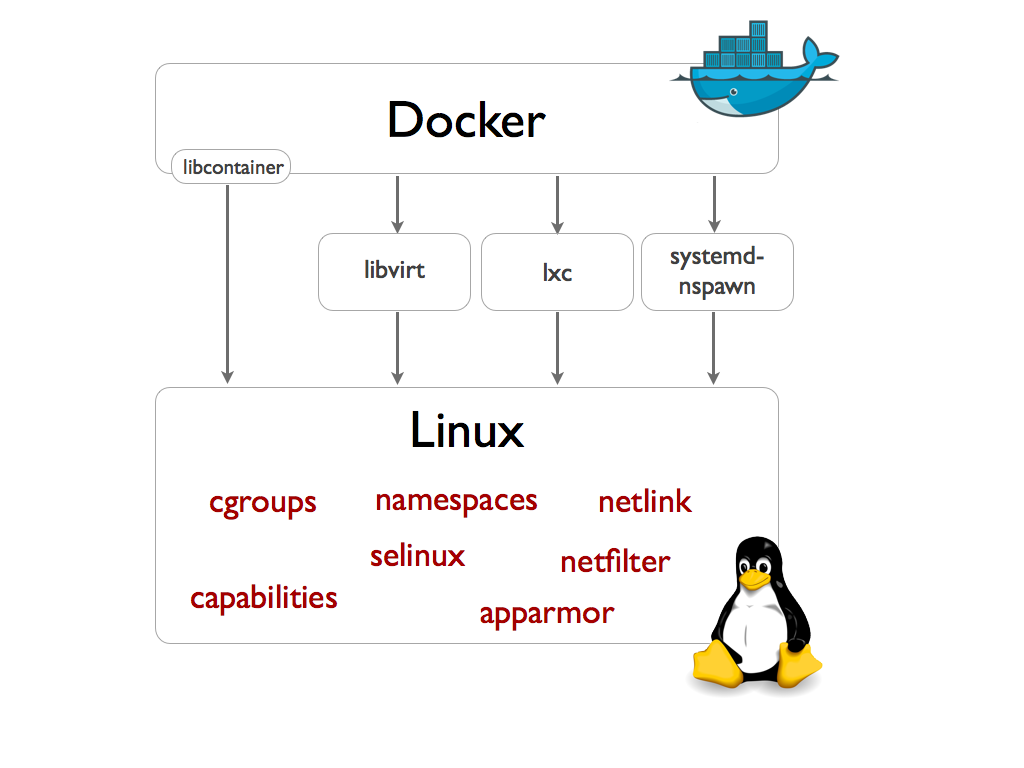
First, we are introducing an execution driver API which can be used to customize the execution environment surrounding each container. This allows Docker to take advantage of the numerous isolation tools available, each with their particular tradeoffs and install base: OpenVZ, systemd-nspawn, libvirt-lxc, libvirt-sandbox, qemu/kvm, BSD Jails, Solaris Zones, and even good old chroot. This is in addition to LXC, which will continue to be available as a driver of its own.
There are already several projects underway to develop more drivers. Want to join the fun? Come say hi on #docker-dev on Freenode, and we’ll help you get started.
New default driver: libcontainer
Second, we are introducing a new built-in execution driver which is shipping alongside the LXC driver. This driver is based on libcontainer, a pure Go library which we developed to access the kernel’s container APIs directly, without any other dependencies.
Thanks to libcontainer, Docker out of the box can now manipulate namespaces, control groups, capabilities, apparmor profiles, network interfaces and firewalling rules – all in a consistent and predictable way, and without depending on LXC or any other userland package. This drastically reduces the number of moving parts, and insulates Docker from the side-effects introduced across versions and distributions of LXC. In fact, libcontainer delivered such a boost to stability that we decided to make it the default. In other words, as of Docker 0.9, LXC is now optional. To switch back to the LXC driver, simply restart the Docker daemon with docker -d -e lxc. Of course we will continue to support the LXC driver going forward.
Using libcontainer for your Go projects
We have developed libcontainer in the hope that other projects will reuse it. If you’re interested in playing with the native container features of Linux – namespaces, cgroups, capabilities etc – then we encourage you to start hacking! To get started go get the Go package and check out the API docs:
go get github.com/dotcloud/docker/pkg/libcontainer godoc github.com/dotcloud/docker/pkg/libcontainer
Objective 1.0
This release is a major step towards a stable, production-ready 1.0 release. We plan on making our next release, 0.10, the first release candidate for 1.0.
As discussed previously, the goals for Docker 1.0 are:
-
production quality
-
first class support of all major operating systems
-
a shrunken core and a stable plug in architecture
-
well documented
-
able to be commercially supported by Docker and our partners
-
Docker able to offer long term support
We are already hard at work preparing 0.10, with several exciting improvements that we think you will like. If you would like a sneak peek, or if you feel like contributing – come say hi! We are on #docker on Freenode. We welcome enthusiasts of all levels and can help you get started with your first contribution. As always, thanks go out to our community of contributors, now 352 strong!
Thanks and happy hacking!
The Docker team